The Growing Importance of Cybersecurity
In an increasingly digital world, cybersecurity has become a critical concern for individuals, businesses, and governments alike. The rise of cyber threats, from data breaches to ransomware attacks, underscores the need for robust security measures. As technology advances, so do the tactics of cybercriminals, making it essential for everyone to stay informed and vigilant.
Recent Cybersecurity Trends
Cybersecurity trends are constantly evolving, driven by technological advancements and the ever-changing threat landscape. Some of the most notable trends include:
- Artificial Intelligence and Machine Learning: These technologies are being used to detect and mitigate cyber threats more efficiently.
- Zero Trust Architecture: This security model assumes that any user or system could be compromised, requiring continuous verification.
- Cloud Security: As more businesses migrate to the cloud, securing cloud environments has become a top priority.
- Internet of Things (IoT) Security: The proliferation of IoT devices has created new vulnerabilities that need to be addressed.
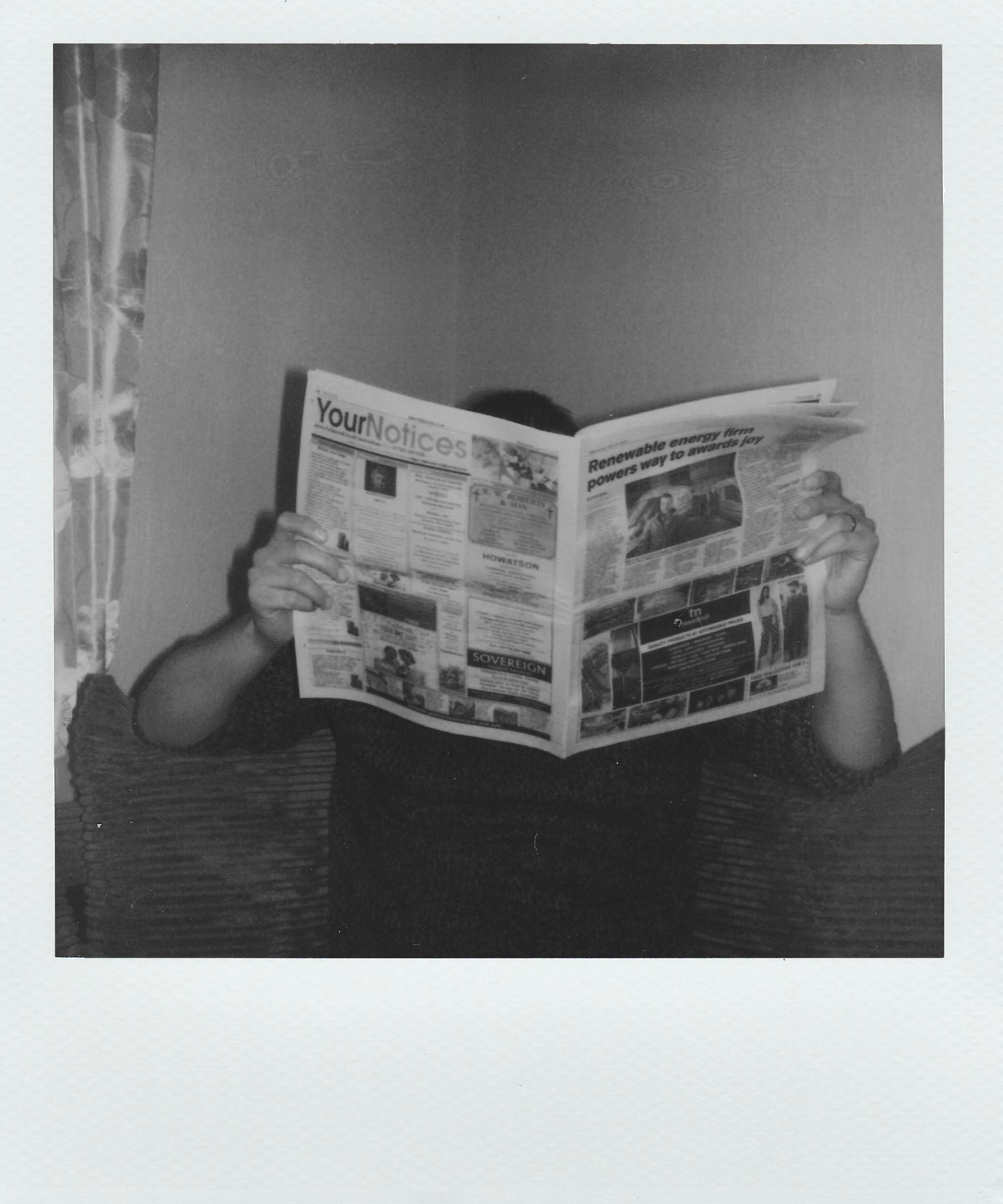
The Role of Local News in Cybersecurity Awareness
Local news outlets play a crucial role in raising awareness about cybersecurity issues. For instance, Austin Texas cybersecurity news and tips provide valuable insights and practical advice for residents and businesses in the area. By staying informed through local news, individuals can better protect themselves against cyber threats.
Cybersecurity Tips for Individuals
While large-scale cyber attacks often make headlines, individuals are also frequent targets of cybercriminals. Here are some essential tips to enhance personal cybersecurity:
- Use Strong, Unique Passwords: Avoid using easily guessable passwords and consider using a password manager.
- Enable Two-Factor Authentication (2FA): This adds an extra layer of security to your accounts.
- Keep Software Up to Date: Regularly update your operating system and applications to patch known vulnerabilities.
- Be Cautious with Emails and Links: Avoid clicking on suspicious links or downloading attachments from unknown sources.
- Use a Virtual Private Network (VPN): A VPN can encrypt your internet connection, making it more secure.
The Impact of Cybersecurity on Businesses
For businesses, the stakes are even higher. A single cyber attack can result in significant financial losses, reputational damage, and legal consequences. To mitigate these risks, businesses should:
- Conduct Regular Security Audits: Identify and address vulnerabilities in your systems.
- Train Employees: Educate staff on best practices for cybersecurity and how to recognize phishing attempts.
- Implement Strong Access Controls: Limit access to sensitive data to only those who need it.
- Develop an Incident Response Plan: Be prepared to respond quickly and effectively to a cyber attack.
Case Studies and Real-World Examples
Real-world examples can provide valuable lessons in cybersecurity. For instance, the 2020 SolarWinds attack highlighted the vulnerabilities in supply chain security, while the 2021 Colonial Pipeline ransomware attack demonstrated the critical importance of protecting infrastructure. These cases underscore the need for proactive cybersecurity measures and continuous vigilance.
The Future of Cybersecurity
The future of cybersecurity is likely to be shaped by advancements in technology and the ongoing arms race between cybercriminals and security experts. Emerging technologies such as quantum computing and blockchain could revolutionize cybersecurity, offering new ways to protect data and systems. However, these advancements also present new challenges and potential vulnerabilities that will need to be addressed.
As the threat landscape continues to evolve, staying informed and proactive is key. By following the latest trends, implementing best practices, and leveraging local resources like Austin Texas cybersecurity news and tips, individuals and businesses can better protect themselves against cyber threats and navigate the complex world of cybersecurity.